Official 2014 Latest Microsoft 70-410 Exam Dump Free Download(331-340)!
QUESTION 331
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. A server named Server1 is configured to encrypt all traffic by using IPSec. You need to ensure that Server1 can respond to ping requests from computers that do not support IPSec. What should you do?
A. From a command prompt, run netsh set global autotuninglevel = restricted congestionprovider = ctcp.
B. From Windows Firewall with Advanced Security, exempt ICMP from IPSec.
C. From a command prompt, run netsh set global
autotuninglevelhighlyrestrictedcongestionprovider=none.
D. From Windows Firewall with Advanced Security, allow unicast responses for the Domain Profile.
QUESTION 332
Hotspot Question
Your network contains an Active Directory domain. The domain contains a server named Server28. The computer account of Server 28 is located in an organizational unit (OU) named OU1. A Group Policy object (GPO) named Application Restriction Policy is linked to OU1. The settings of the GPO are configured as shown in the GPO Settings exhibit. (Click the Exhibit button.)
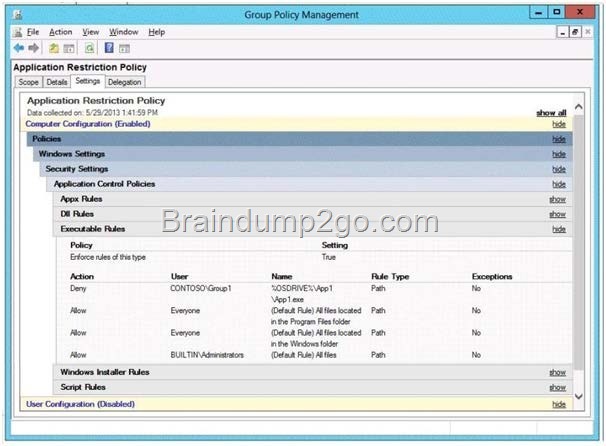
The Services console on Server28 is shown in the Services exhibit. (Click the Exhibit button.)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0014_thumb.jpg)
Select Yes if the statement can be shown to be true based on the available information; otherwise select No. Each correct selection is worth one point.
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0016_thumb.jpg)
Answer:
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0024_thumb.jpg)
QUESTION 333
Drag and Drop Question
You have a Hyper-V host named Server1. Server1 hosts a virtual machine named VM1. You view the properties of VM1 as shown in the following exhibit. (Click the Exhibit button.)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0018_thumb.jpg)
You need to configure bandwidth management for VM1. Which three actions should you perform in sequence? (To answer, move the appropriate three actions from the list of actions to the answer area and arrange them in the correct order.)
QUESTION 334
You plan to deploy a file server to a temporary location. The temporary location experiences intermittent power failures. The file server will contain a dedicated volume for shared folders. You need to create a volume for the shared folders. The solution must minimize the likelihood of file corruption if a power failure occurs. Which file system should you use?
A. ReFS
B. NFS
C. NTFS
D. FAT32
Answer: A
Explanation:
The ReFS file system allows for resiliency against corruptions with the option to salvage amongst many other key features like Metadata integrity with checksums, Integrity streams with optional user data integrity, and shared storage pools across machines for additional failure tolerance and load balancing, etc.
QUESTION 335
Your company has a main office and four branch offices. The main office contains a server named Server1 that runs Windows Server 2012 R2. The IP configuration of each office is configured as shown in the following table.
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00112_thumb.jpg)
You need to add a single static route on Server1 to ensure that Server1 can communicate with the hosts on all of the subnets. Which command should you run?
A. route.exe add -p 10.10.0.0 mask 255.255.252.0 10.10.0.1
B. route.exe add -p 172.16.16.0 mask 255.255.252.0 10.10.0.1
C. route.exe add -p 10.10.0.0 mask 255.255.252.0 172.16.0.0
D. route.exe add -p 172.16.18.0 mask 255.255.252.0 10.10.0.1
Answer: B
Explanation:
These parameters will allow communication with all the hosts.
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00114_thumb.jpg)
QUESTION 336
You work as a senior administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers on the L2P.com network have Windows Server 2012 R2 installed.
You are running a training exercise for junior administrators. You are currently discussing what happens when you run the Remove-NetLbfoTeam Windows PowerShell cmdlet.
Which of the following describes the results of running this cmdlet?
A. It removes one or more network adapters from a specified NIC team.
B. It removes a team interface from a NIC team.
C. It removes a specified NIC team from the host.
D. It removes a network adapter member from a switch team.
Answer: C
Explanation:
Remove-NetLbfoTeam removes the specified NIC team from the host
The Remove-NetLbfoTeam cmdlet removes the specified NIC team from the host. This cmdlet disconnects all associated team members and providers from the team. You can specify the team to remove by using either a team object retrieved by Get-NetLbfoTeam, or by specifying a team name.
You can use Remove-NetLbfoTeam to remove all NIC teams from the server.
You need administrator privileges to use Remove-NetLbfoTeam.
http://technet.microsoft.com/en-us/library/jj130848%28v=wps.620%29.aspx
QUESTION 337
You work as a senior administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers in the L2P.com domain, including domain controllers, have Windows Server 2012 R2 installed.
You are running a training exercise for junior administrators. You are currently discussing the Virtual Fibre Channel SAN feature.
Which of the following is TRUE with regards to the Virtual Fibre Channel SAN feature? (Choose all that apply.)
A. It prevents virtual machines from connecting directly to Fibre Channel storage.
B. It allows for virtual machines to connect to Fibre Channel storage directly.
C. It includes support for virtual SANs, live migration, and multipath I/O.
D. It includes support for virtual SANs, and live migration, but not multipath I/O.
Answer: BC
Explanation:
To gain the full benefits of server virtualization and cloud architectures, virtualized workloads need to connect easily and reliably to existing SANs. For many enterprise organizations, Hyper-V deployments were limited in scale and scope because they
lacked the ability to directly connect VMs to Fibre Channel SAN storage from inside a VM. Hyper-V in Windows Server 2012 R2 now provides virtual Fibre Channel Host Bus Adapter (HBA) ports within the guest operating system that runs the virtual machine, connecting virtual machines directly to FibreChannel SAN Logical Unit Numbers (LUNs).
Virtual Fibre Channel for Hyper-V provides several important advantages for Hyper-V environments:
Simplifies storage connectivity for virtualized workloads to ultra-reliable, high-performance Fibre Channel SAN storage
Enables new solutions that require shared storage, such as failover clustering, live migration, andmultipath I/O
Leverages and protects existing investments in Fibre Channel storage ?
Enables advanced FC SAN storage functionality for VMs
Facilitates migration of FC workloads into the cloud
Enables improved monitoring and troubleshooting, with visibility from the VM to the FC SAN storage
Enables centralized management of Ethernet and FC-based virtualized workloads
Combining Virtual Fibre Channel for Hyper-V and the Brocade?Fibre Channel SAN infrastructure greatly simplifies connectivity between Fibre Channel SAN storage and virtualized applications, enabling enterprise IT and hosting providers to achieve new levels of availability, reliability, and scalability for cloud-based services.
You need your virtualized workloads to connect easily and reliably to your existing storage arrays. Windows Server 2012 R2 provides Fibre Channel ports within the guest operating system, which allows you to connect to Fibre Channel directly from within virtual machines. This feature protects your investments in Fibre Channel, enables you to virtualize workloads that use direct access to Fibre Channel storage, allows you to cluster guest operating systems over Fibre Channel, and provides an important new storage option for servers hosted in your virtualization infrastructure.
With this Hyper-V virtual Fibre Channel feature, you can connect to Fibre Channel storage from within a virtual machine. This allows you to use your existing Fibre Channel investments to support virtualized workloads. Support for Fibre Channel in Hyper-V guests also includes support for many relatedfeatures, such as virtual SANs, live migration, and MPIO.
http://technet.microsoft.com/en-us/library/hh831413.aspx
http://www.brocade.com/downloads/documents/technical_briefs/virtual-fibre-channel-hyperv-tb.pdf
QUESTION 338
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. On a server named Server2, you perform a Server Core Installation of Windows Server 2012 R2.
You join Server2 to the contoso.com domain. You need to ensure that you can manage Server2 by using the Computer Management console on Server1. What should you do on Server2?
A. Install Remote Server Administration Tools (RSAT).
B. Install Windows Management Framework.
C. Run sconfig.exe and configure remote management.
D. Run sconfig.exe and configure Remote Server Administration Tools (RSAT).
Answer: C
Explanation:
In Windows Server 2012 R2, you can use the Server Configuration tool (Sconfig.cmd) to configure and manage several common aspects of Server Core installations. You must be a member of the Administrators group to use the tool. Sconfig.cmd is available in the Minimal Server Interface and in Server with a GUI mode.
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0028_thumb.jpg)
QUESTION 339
You work as an administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers in the L2P.com domain, including domain controllers, have Windows Server 2012 R2 installed.
When you recently added new workstations to the L2P.com manually, you found that that the computer accounts were created in the default container. You want to make sure that the default container for newly created computers is redirected to a specified, target organizational unit (OU).
Which of the following actions should you take?
A. You should consider making use of the replace.exe command-line tool.
B. You should consider making use of the redircmp.exe command-line tool.
C. You should consider making use of the redirusr.exe command-line tool.
D. You should consider making use of the rexec.exe command-line tool.
Answer: B
Explanation:
redircmp.exe redirects the default container for newly created computers to a specified, targetorganizational unit (OU) so that newly created computer objects are created in the specific target OU instead of in CN=Computers.
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00210_thumb.jpg)
http://technet.microsoft.com/pt-pt/library/cc770619%28v=ws.10%29.aspx http://support.microsoft.com/kb/324949/en-us
http://support.microsoft.com/kb/555573/en-us
QUESTION 340
You work as an administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com.
L2P.com has a Windows Server 2012 R2 domain controller, named L2P-DC01, which has the Domain Naming master and the Schema master roles installed. L2P.com also has a Windows Server 2008 R2 domain controller, named L2P-DC02, which has the PDC Emulator, RID master, and Infrastructure master roles installed.
You have deployed a new Windows Server 2012 server, which belongs to a workgroup, in L2P.com’s perimeter network. You then executed the djoin.exe command.
Which of the following is the purpose of the djoin.exe command?
A. It sets up a computer account in a domain and requests an offline domain join when a computer restarts.
B. It sets up a user account in a domain and requests an online domain join when a computer restarts.
C. It sets up a computer account in a domain and requests an offline domain join immediately.
D. It sets up a computer account in a domain and requests an online domain join immediately.
Answer: A
Explanation:
To perform an offline domain join, you run commands by using a new tool named Djoin.exe. You use Djoin.exe to provision computer account data into AD DS. You also use it to insert the computer account data into the Windows directory of the destination computer, which is the computer that you want to join to the domain.
/localos Targets the local operating system installation, instead of an offline image, with the domain join information. Because this parameter injects the blob data into the locally running operating system image, you must restart the computer to complete the domain join operation, as you must also do for an onlinedomain join.
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00212_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00118_thumb.jpg)
http://technet.microsoft.com/en-us/library/offline-domain-join-djoin-step-by-step%28v=ws.10%29.aspx
Passing Microsoft 70-410 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-410 Dump:

![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image00110_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/8bae56556d4d_7B35/clip_image0026_thumb.jpg)